The Hardware Security Modules (HSM) market is witnessing significant growth as organizations prioritize data protection, secure cryptographic key management, and regulatory compliance. With cyber threats becoming more sophisticated and digital transactions rapidly increasing across industries, businesses are turning to HSMs to safeguard sensitive information and strengthen their cybersecurity infrastructure.
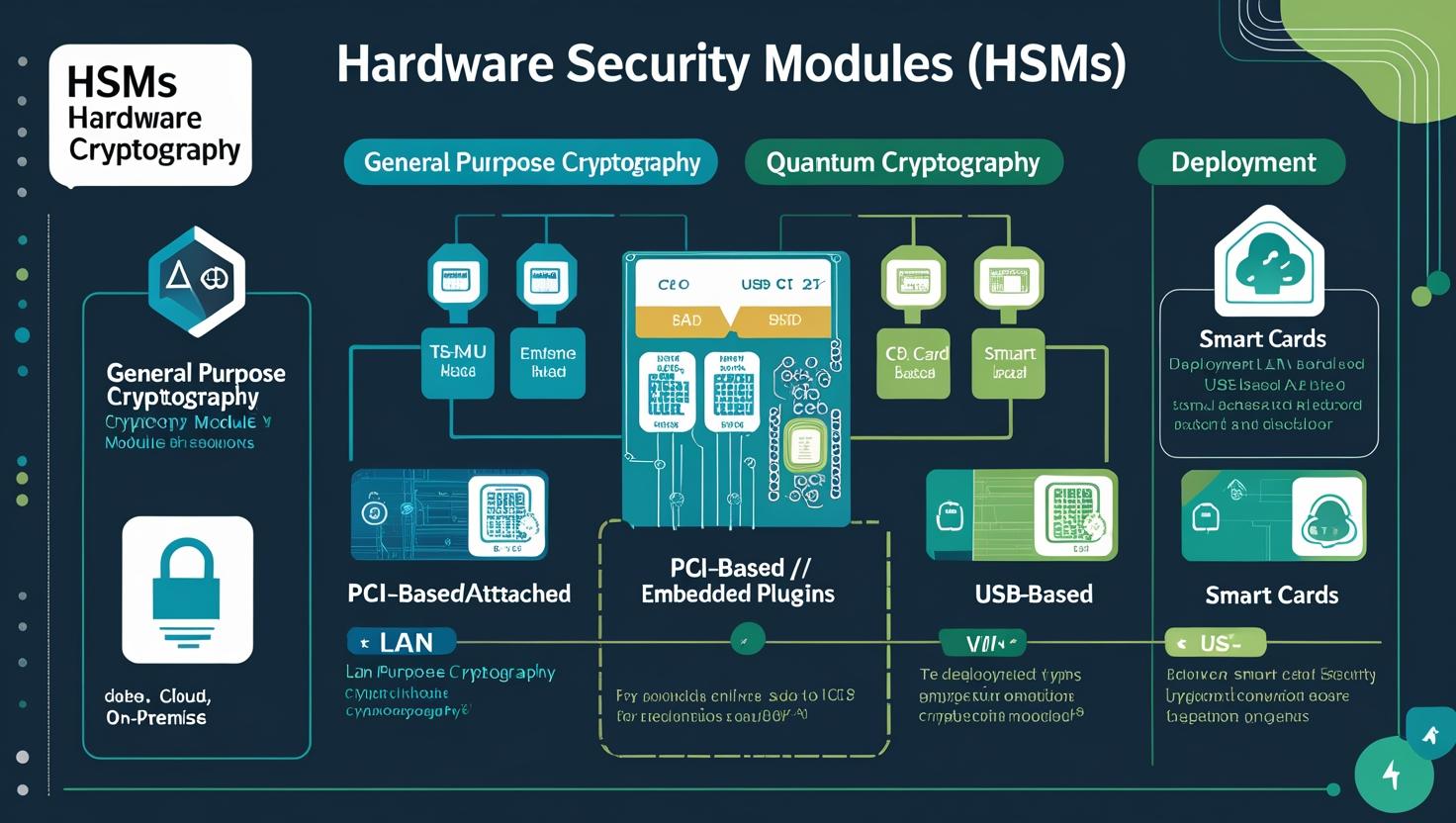
Hardware Security Modules are specialized physical devices designed to generate, store, and manage cryptographic keys securely. These systems provide a tamper-resistant environment that protects encryption keys and performs critical cryptographic operations such as encryption, decryption, authentication, and digital signing. As organizations increasingly rely on encryption to protect data across cloud platforms, payment systems, and enterprise networks, the demand for HSM solutions continues to rise.
Growing Importance of Secure Key Management
One of the key drivers of the Hardware Security Modules market is the growing need for robust key management systems. Encryption plays a central role in protecting digital assets, but the effectiveness of encryption largely depends on how securely cryptographic keys are managed. Weak key management practices can expose sensitive data to breaches, making secure key storage and lifecycle management essential.
HSMs address this challenge by providing dedicated hardware environments that prevent unauthorized access to cryptographic keys. They ensure that keys remain protected throughout their lifecycle, from generation and storage to distribution and deletion. As organizations adopt advanced technologies such as cloud computing, Internet of Things (IoT), and digital identity solutions, the complexity of managing encryption keys increases—further strengthening the need for reliable HSM platforms.
Additionally, enterprises are implementing encryption across multiple environments, including on-premises infrastructure, hybrid cloud systems, and public cloud platforms. HSMs provide a centralized and secure method to manage encryption keys across these environments, enabling businesses to maintain strong security policies while ensuring operational efficiency.
Download PDF Brochure @ https://www.marketsandmarkets.com/pdfdownloadNew.asp?id=162277475
Regulatory Compliance Driving Market Adoption
Regulatory requirements are another major factor fueling the growth of the Hardware Security Modules market. Governments and regulatory bodies worldwide are introducing stricter rules related to data privacy, payment security, and digital identity protection. Compliance standards often require organizations to use secure cryptographic solutions to protect sensitive information.
Industries such as banking, financial services, healthcare, and government agencies must comply with strict regulations regarding the protection of personal and financial data. HSMs help organizations meet these compliance requirements by offering certified security standards, secure key management, and reliable cryptographic processing.
For example, payment security regulations require financial institutions and payment processors to protect cardholder data and maintain strong encryption practices. HSMs play a critical role in enabling secure payment processing, PIN management, and transaction authentication. As digital banking, online payments, and mobile transactions continue to expand globally, the need for trusted encryption infrastructure is becoming increasingly essential.
Expanding Use Cases Across Industries
While the financial sector has traditionally been the largest adopter of HSM technology, other industries are rapidly integrating these solutions into their security frameworks. Healthcare organizations are using HSMs to protect electronic health records and ensure compliance with healthcare data protection regulations. Government agencies rely on HSMs for digital identity programs, secure communication systems, and national security applications.
In addition, enterprises operating in sectors such as telecommunications, manufacturing, and retail are deploying HSMs to protect sensitive operational data and secure connected devices. The rapid growth of IoT ecosystems has further increased the need for secure key provisioning and device authentication—areas where HSMs play a vital role.
Integration with Cloud Security Platforms
The increasing adoption of cloud computing has transformed how organizations deploy and manage security infrastructure. To address evolving cloud security challenges, vendors are offering cloud-based HSM services that enable businesses to manage cryptographic keys securely without maintaining physical hardware.
Cloud HSM solutions provide scalability, flexibility, and remote management capabilities while maintaining the high level of security associated with traditional HSM devices. Enterprises adopting multi-cloud strategies are particularly benefiting from cloud-integrated HSM services, which help maintain consistent encryption policies across multiple cloud environments.
As organizations migrate critical workloads to the cloud, integrating HSMs into cloud security architectures is becoming an essential component of enterprise cybersecurity strategies.
Technological Advancements Enhancing HSM Capabilities
Technological innovations are also shaping the evolution of the Hardware Security Modules market. Modern HSMs are designed to support high-performance cryptographic processing, enabling them to handle large volumes of secure transactions in real time. Advanced models now support a wide range of encryption algorithms and security protocols required by modern digital systems.
In addition, vendors are developing next-generation HSM solutions that support emerging technologies such as blockchain, digital identity management, and secure DevOps environments. These advancements allow organizations to integrate cryptographic security seamlessly into modern application development and digital infrastructure.
Market Outlook
Looking ahead, the Hardware Security Modules market is expected to continue its steady expansion as cybersecurity threats grow and digital transformation accelerates across industries. The increasing reliance on encryption, stricter regulatory frameworks, and the rise of cloud computing are all contributing to the growing demand for secure cryptographic infrastructure.
Organizations are recognizing that strong encryption alone is not sufficient without proper key protection. As a result, HSMs are becoming a critical component of modern cybersecurity strategies, helping businesses safeguard sensitive data, maintain regulatory compliance, and build trust in digital systems.
With the ongoing evolution of digital services, financial technologies, and connected devices, Hardware Security Modules will remain an essential technology for ensuring secure digital operations in the years ahead.
Frequently Asked Questions (FAQs)
1. What is a Hardware Security Module (HSM)?
A Hardware Security Module (HSM) is a dedicated physical device designed to securely generate, store, and manage cryptographic keys. It performs encryption, decryption, authentication, and digital signing operations within a highly secure, tamper-resistant environment to protect sensitive data.
2. Why are Hardware Security Modules important for cybersecurity?
HSMs play a critical role in cybersecurity by safeguarding cryptographic keys used in encryption processes. By isolating keys within a secure hardware environment, HSMs reduce the risk of unauthorized access, data breaches, and cyberattacks targeting sensitive information.
3. Which industries use Hardware Security Modules the most?
Several industries rely heavily on HSM technology, including banking and financial services, healthcare, government, telecommunications, and retail. These sectors require strong encryption and secure key management to protect sensitive customer and operational data.
4. How do Hardware Security Modules help with regulatory compliance?
HSMs help organizations meet strict regulatory requirements related to data security and privacy. Many compliance standards require secure cryptographic key management and certified encryption processes, which HSMs are designed to provide.
5. What is the difference between cloud HSM and on-premises HSM?
On-premises HSMs are physical devices installed within an organization’s infrastructure, offering direct control over cryptographic operations. Cloud HSMs, on the other hand, are managed services provided through cloud platforms that allow organizations to access secure key management without maintaining physical hardware.
